Research & Reference Services

Getting Set Up To Use The Internet
The function of this paper is to report on an exploratory examine which examined the perspectives of the student interns and the undergraduate scholar purchasers, in order to illuminate advantages and challenges that emerged. Twenty-four MSW student interns and 34 undergraduate student shoppers who utilized cyber counseling on no less than one occasion participated in interviews that had been transcribed and analyzed. Both the MSW interns and the undergraduate student purchasers reported that cyber counseling provided sensible and relational value and that the written aspect was particularly helpful in facilitating clients’ disclosure of sensitive points. Different views about maintaining connection within the relationship emerged, suggesting challenges for social staff when studying to make use of cyber in counseling. Department of Education on college students’ entry to digital learning exterior of college is now public.
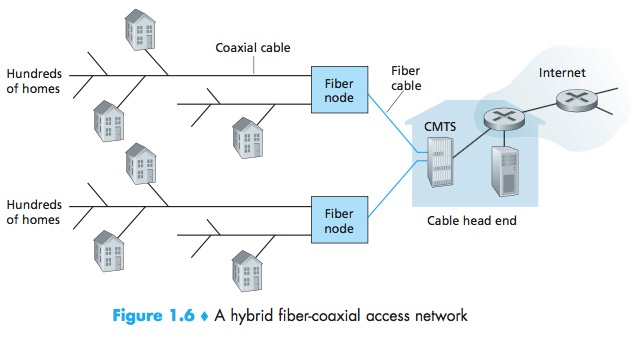
Another commonality is that many of the applied sciences, besides maybe for digital games, are designed primarily to promote interplay and collaboration with others. Our search yielded only a few studies on how informational applied sciences, such as video lectures and podcasts, affect student engagement. Unlike the technologies we identified earlier, informational applied sciences reflect a behaviorist approach to studying during which college students are passive recipients of knowledge that’s transmitted from an professional (Boghossian, 2006). A new technology referred to as broadband over fiber (BoF) is a direct connection option for internet entry. Internet service providers are starting to adopt this new expertise and sell it for a …