Computer and Internet Safety
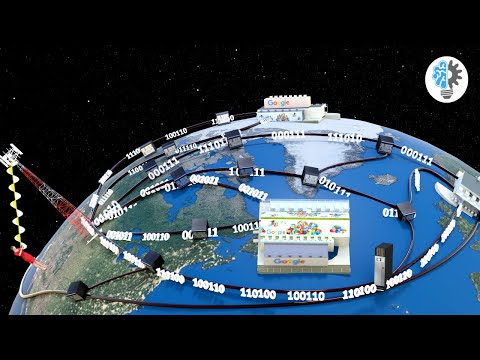
The last restrictions on carrying commercial site visitors ended on 30 April 1995, when the NSF ended its sponsorship of the NSFNET Backbone Service and the service ended. Today virtually all Internet infrastructure within the United States, and large portion in other international locations, is supplied and owned by the personal sector. Traffic is exchanged between these networks, at main interconnection factors, in accordance with established Internet requirements and business agreements. National Science Foundation (NSF) created the NSFNET backbone, utilizing TCP/IP, to attach their supercomputing amenities. NSFNET turned a common-purpose analysis community, a hub to connect the supercomputing facilities to one another and to the regional analysis and schooling networks that would in flip connect campus networks.
In current examine, Mangen, Walgermo, and Bronnick found that college students who read on paper carried out slightly higher than those who read an e-e-book on an open-e-book reading comprehension exam of multiple-alternative and short-answer questions. While a meta-evaluation of analysis by Andrews seemed to confirm that people read extra slowly and comprehend much less when reading from screens, a meta-analysis of newer analysis on this topic does not present something definite (Noyes and Garland 2008).
While a telephone is a two-way communication device, mass media communicates to a big group. In addition, the telephone has remodeled into a cell phone which is provided with Internet access. A question arises whether this makes cell telephones a mass medium or just a tool used to entry a mass medium (the Internet).
An internet service …

